In today’s interconnected business landscape, very few organizations operate in isolation. From cloud service providers and payment processors to marketing agencies and supply chain partners, businesses increasingly rely on an intricate web of external entities to deliver their products and services. While these partnerships are essential for innovation, efficiency, and growth, they also introduce a significant — and often underestimated — layer of risk. Disruption, data breaches, and reputational damage stemming from a third party can ripple through an organization, impacting everything from customer trust to regulatory compliance.
Navigating this complex ecosystem requires more than just good intentions or ad-hoc checks. It demands a structured, comprehensive approach to identify, assess, mitigate, and monitor the risks posed by your vendors, suppliers, and partners. This is precisely where a well-conceived Third Party Risk Management Program Template becomes an invaluable asset, offering a systematic framework to safeguard your organization’s assets, data, and reputation in an increasingly outsourced world. It’s about building resilience, ensuring compliance, and fostering sustainable growth in a landscape defined by collaboration.
The Unseen Web: Why Third-Party Risk Management is Non-Negotiable
The headlines are rife with examples of organizations suffering severe consequences due to the security lapses or operational failures of their third parties. A data breach originating from a vendor can lead to millions in fines, damaged customer loyalty, and a precipitous drop in stock value. Similarly, a critical service provider experiencing an outage can halt operations, causing significant financial losses and reputational harm. The reality is that your risk perimeter extends far beyond your organizational walls, encompassing every entity that touches your data, systems, or operations.
A robust approach to managing third-party risks isn’t just a best practice; it’s a fundamental requirement for maintaining business continuity and integrity. Regulators across various industries, from finance to healthcare, are intensifying their scrutiny of how organizations manage their external relationships. Compliance mandates like GDPR, CCPA, HIPAA, and various industry-specific regulations often include explicit requirements for overseeing third-party security and data handling practices. Failing to meet these expectations can result in hefty penalties, legal challenges, and a loss of public trust that can take years to rebuild.
Beyond Compliance: The Strategic Advantages of a Robust Program
While compliance is a significant driver, the benefits of a well-structured third-party governance framework extend far beyond simply avoiding penalties. Implementing a comprehensive program for managing external entity risks transforms a necessary chore into a strategic advantage. It provides clarity and control over your entire vendor ecosystem, allowing for more informed decision-making and better resource allocation.
By systematically identifying and evaluating risks, organizations can prioritize their efforts, focusing on the most critical vendors and the most significant threats. This proactive stance helps in negotiating stronger contracts with appropriate security clauses and service level agreements (SLAs), fostering more secure and reliable partnerships from the outset. Ultimately, a strong vendor risk management program contributes to operational resilience, enhances overall security posture, and strengthens the trust of customers, investors, and stakeholders. It’s an investment in long-term stability and sustainable growth.
Key Components of an Effective Third-Party Risk Management Framework
Developing a comprehensive program for external risk oversight involves integrating various processes, technologies, and people across the organization. It’s not a one-time project but a continuous lifecycle that spans the entire relationship with a third party, from initial engagement to eventual offboarding. At its core, an effective framework for managing third-party risks typically encompasses several critical stages and foundational elements.
The journey often begins with an initial due diligence phase, where potential vendors are thoroughly vetted before any contract is signed. This involves assessing their security posture, financial stability, compliance history, and operational capabilities. Once a vendor is engaged, contractual agreements must explicitly define security expectations, audit rights, and incident response procedures. Ongoing monitoring is then crucial to ensure continuous adherence to these agreements and to identify any emerging risks. Finally, a structured exit strategy ensures that data is securely returned or destroyed, and access is revoked when a relationship concludes.
Building Your Own: Tailoring a Third Party Risk Management Program Template to Your Needs
While the principles of managing third-party risks are universal, the specific implementation needs to be tailored to your organization’s unique context, risk appetite, and resources. There’s no one-size-fits-all solution, but a well-designed Third Party Risk Management Program Template provides a powerful starting point. It offers a structured foundation that you can adapt, scale, and refine to fit your specific industry, regulatory environment, and the complexity of your vendor ecosystem.
When beginning this journey, resist the urge to tackle every single vendor simultaneously. Start by identifying your most critical third parties—those that handle sensitive data, provide essential services, or pose the highest potential impact if compromised. Implement a tiered approach where vendors are categorized based on their inherent risk profile, allowing you to apply appropriate levels of scrutiny. Ownership and accountability for different aspects of the program must be clearly defined across relevant departments, including legal, procurement, IT, and security. Consider leveraging technology solutions, from simple spreadsheets to dedicated TPRM platforms, to automate assessments, track responses, and manage the lifecycle efficiently as your program matures.
Essential Elements for Your Program’s Success
To effectively implement and mature your external risk framework, focus on integrating these fundamental components into your operations. These elements form the backbone of a resilient and compliant program, ensuring a structured and consistent approach to managing your extended enterprise.
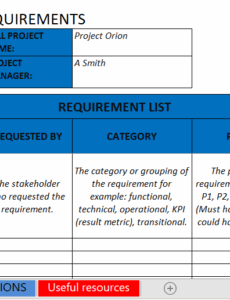
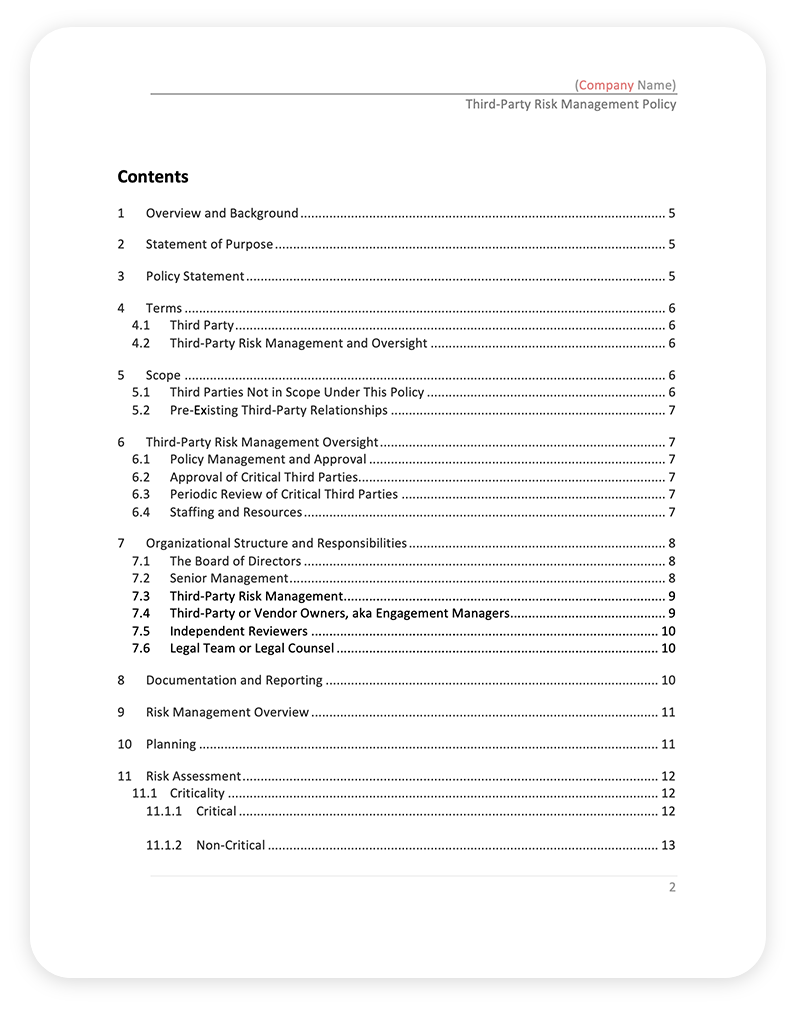
- Clear Policies and Procedures: Establish comprehensive documents outlining the scope, roles, responsibilities, and methodologies for identifying, assessing, mitigating, and monitoring third-party risks. These policies should define what constitutes a third party and the various stages of the risk management lifecycle.
- Comprehensive Vendor Inventory: Maintain an up-to-date and centralized list of all your third parties, including contact information, services provided, criticality, and the type of data they access or process. Knowing your ecosystem is the first step in managing it.
- Risk Assessment Methodology: Develop a consistent and repeatable process for evaluating inherent risks (before controls) and residual risks (after controls) associated with each third party. This should include standardized questionnaires, security assessments, and potentially on-site audits for high-risk vendors.
- Contractual Safeguards: Ensure that all contracts with third parties include robust clauses addressing data security, privacy, incident response, audit rights, compliance requirements, and liability. These clauses are your legal backbone in managing risk.
- Ongoing Monitoring and Performance Management: Implement continuous or periodic monitoring mechanisms to assess a third party’s performance and adherence to agreed-upon security and compliance standards. This can include reviewing security reports, incident logs, and service level attainment.
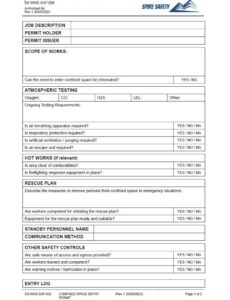
- Incident Response and Business Continuity Planning: Establish clear protocols for how your organization and your third parties will respond to security incidents or business disruptions. Ensure that your third parties have adequate business continuity and disaster recovery plans in place.
- Regular Review and Continuous Improvement: Your vendor risk management program is not static. Periodically review its effectiveness, update policies and procedures to reflect new threats or regulations, and incorporate lessons learned from incidents or assessments.
Navigating the Landscape: Best Practices and Common Pitfalls
Successfully implementing a comprehensive supplier risk management strategy requires vigilance and a commitment to continuous improvement. One common pitfall is treating all third parties equally; remember to tier your vendors based on risk and criticality. High-risk vendors handling sensitive data or providing essential services warrant more intensive scrutiny than a low-risk office supply vendor. Another mistake is relying solely on self-assessment questionnaires without independent verification or evidence. While questionnaires are a good starting point, they should be supplemented with external security ratings, certifications, or even on-site audits where appropriate.
Integrate your third-party risk efforts with other organizational risk functions, such as enterprise risk management, information security, and compliance. This holistic view ensures that external risks are considered within the broader organizational context and helps avoid silos. Furthermore, foster a risk-aware culture throughout your organization. Educate employees who interact with third parties on their role in identifying and reporting potential risks, emphasizing that external relationships are a shared responsibility. By focusing on these best practices and proactively avoiding common missteps, you can significantly enhance the resilience and security of your extended enterprise.
Embracing a structured approach to third-party risk isn’t merely about avoiding negative consequences; it’s about empowering your organization to innovate and grow with confidence. By implementing a robust program, you transform potential vulnerabilities into managed risks, allowing you to fully leverage the benefits of external partnerships without compromising your security posture or reputation. It’s an investment in strategic foresight, operational integrity, and long-term organizational health.
The journey to mature your third-party risk management capabilities may seem daunting, but starting with a solid framework and adapting it to your specific needs will yield significant returns. Begin by assessing your current state, identifying critical gaps, and leveraging a foundational Third Party Risk Management Program Template to guide your initial steps. With dedication and a commitment to continuous improvement, your organization can build a resilient and secure ecosystem that supports your strategic objectives well into the future.